Id-Logon
and information systems by facial recognition
Id-Logon checks for the user’s access rights to a PC or an information system by face and can serve as the main or additional verification factor in the following scenarios:
- Windows OS authentication
- Two-factor authentication
- Access to various applications
- Employee presence control at PC
- Blocking unauthenticated PC users
SOLUTION ADVANTAGES
of the camera is real
the installation package
WHAT BENEFITS DOES THE ID-logon USER GET?
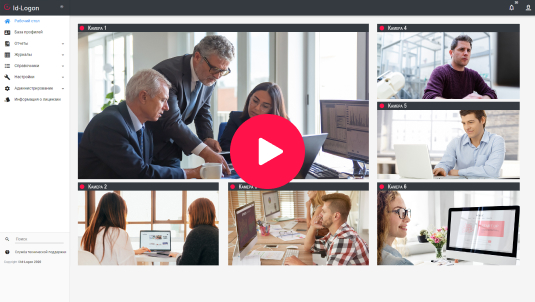
Tools for secure checking access rights to a PC using web and IP cameras:
AUTHENTICATION in the system by face eliminates unauthorized access to OS or IS of enterprise infrastructure with someone else’s account credentials
FACIAL AUTHENTICATION makes using passwords unnecessary while maintaining high security level and increasing user convenience
FOR WORKPLACES without computers, presence check of employees may be implemented with the help of IP cameras
FACIAL BIOMETRICS is used on the client side and is not sensitive to interferences arising in external channels
THE SOLUTION RECOGNIZES an intruder by face
and automatically blocks their access to the system
SOLUTION CHECKS the presence of an employee at their workplace according to the set parameters and promptly notifies security if any accident occurs
How DOES it work?
with the help of an installer
to install Id-Logon
DEMO LICENSE
A free demo license is provided for 3 months to experience all the functionality of the solution
at your facility.
For a demo, please fill out a request or contact our team at sales@recfaces.com.

IDENTIFICATION ALGORITHMS ARE GETTING BETTER
We are constantly improving Id-Logon and other solutions, making recognition systems more accurate and faster. Each updated release includes new functional and technological options that make the users’ work more convenient and efficient.
The support certificate includes software updates and technical support.
User authentication with facial biometrics
A solution that provides easy and reliable authentication by face in operating systems or enterprise applications, as well as reliable presence check
of authorized employees at their workplaces.